Windows 7 Repair virus would readily control thoughts of its users, most of which suspect the program is not quite fair. In fact, the program is a shameless faker that does not hesitate to inform users of threats and errors that have never existed or exist somewhere but have not been detected in the memory it pretends to inspect.
The program-faker tries to foresee user’s thoughts in relation to its words and thus to predict the response. According to the user’s response prediction, the adware follows more or less obtrusive schedule. More inclined to remove Windows 7 Repair users would see less frequent popups, and vice versa, more patient users would suffer more headache with the adware popups.
Needless to say, the adware is not a prophet so that it often fails to correctly assess user’s attitude to its alerts. Anyway, all the users sooner or later arrive at one and same conclusion that they need to get rid of Windows 7 Repair.
Click here to instantly launch free scanner and remove Windows 7 Repair as the program is but yet another annoying prosecutor of dummy infections.
The program-faker tries to foresee user’s thoughts in relation to its words and thus to predict the response. According to the user’s response prediction, the adware follows more or less obtrusive schedule. More inclined to remove Windows 7 Repair users would see less frequent popups, and vice versa, more patient users would suffer more headache with the adware popups.
Needless to say, the adware is not a prophet so that it often fails to correctly assess user’s attitude to its alerts. Anyway, all the users sooner or later arrive at one and same conclusion that they need to get rid of Windows 7 Repair.
Click here to instantly launch free scanner and remove Windows 7 Repair as the program is but yet another annoying prosecutor of dummy infections.
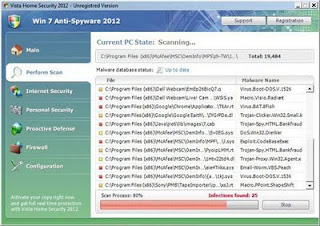
Windows 7 Repair snapshot:
Manual removal information (guide):
Delete infected files:
%AllUsersProfile%\
%AllUsersProfile%\.exe
%AllUsersProfile%\~
%AllUsersProfile%\~
%StartMenu%\Programs\Windows 7 Repair\
%StartMenu%\Programs\Windows 7 Repair\Uninstall Windows 7 Repair.lnk
%StartMenu%\Programs\Windows 7 Repair\Windows 7 Repair.lnk
Delete infected registry entries:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run ".exe"
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run ""
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings "CertificateRevocation" = '0'
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings "WarnonBadCertRecving" = '0'
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\ActiveDesktop "NoChangingWallPaper" = '1'
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Associations "LowRiskFileTypes" = '/{hq:/s`s:/ogn:/uyu:/dyd:/c`u:/bnl:/ble:/sdf:/lrh:/iul:/iulm:/fhg:/clq:/kqf:/`wh:/lqf:/lqdf:/lnw:/lq2:/l2t:/v`w:/rbs:'
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Attachments "SaveZoneInformation" = '1'
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System "DisableTaskMgr" = '1'
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system "DisableTaskMgr" = '1'
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Download "CheckExeSignatures" = 'no'
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main "Use FormSuggest" = 'yes'
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced "Hidden" = '0'
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced "ShowSuperHidden" = 0'